Protect Yourself from Phishing Scams

From impersonating people we already know and trust to portraying companies we do business with, there’s no shortage of phishing scams in ever-growing numbers. With each passing day, scammers seem to grow more advanced, evolving with each sophistication we make in technology. They utilize various strategies to deceive and extract users’ private information or credentials or, at the very least, some money. This guide outlines different phishing strategies and how one can shield oneself. We will focus on explaining the key red flags to help you remain safe online. Additionally, we will address crucial practices concerning email security.
Identifying The Fraudulent Google Docs Invite
Many of us use platforms such as Google Docs for sharing documents because it is convenient and collaborative. Unfortunately, this convenience makes it one of the primary targets for phishing scams. Let us assume you received an email notifying you of an invitation to edit a document. With further analysis, it turns out to be a well-planned and executed attempt to acquire your login details or even worse, to install a piece of malware. Let us simplify how you can help to not fall victim to these scams.
Example Phishing Scenario:
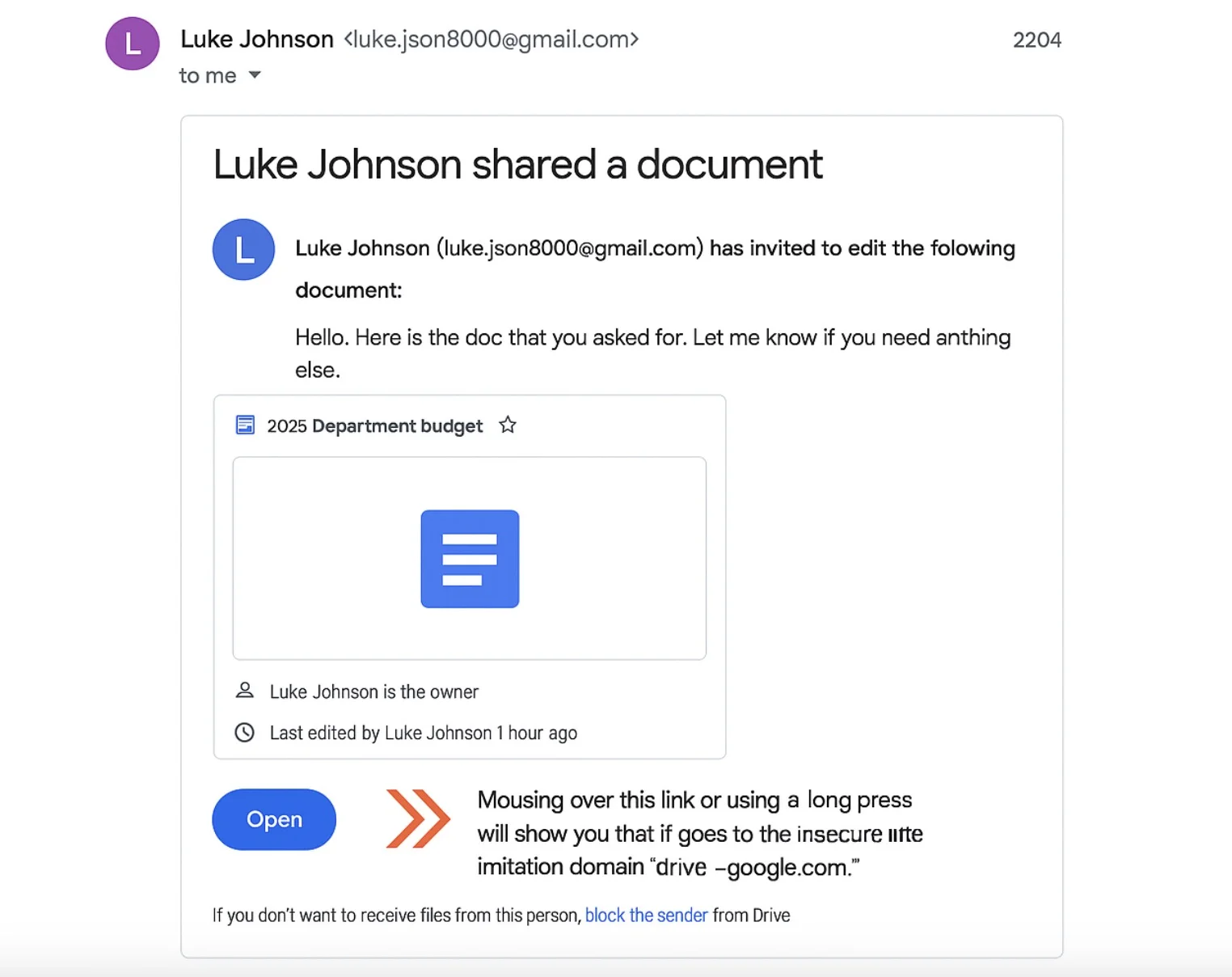
You have received an invite to edit a Google Document titled “2025 Department Budget” which appears to be shared by “Luke Johnson”. Are you sure that Luke is the one who invited you? Also, is the link provided safe?
How to Detect a Phishing Scam:
- Check the Email Address of the Sender (Very Carefully): Scammers impersonate people easily, so do not stare at the name blindly. In this case, mousing over this link or using a long press will show you that it goes to the insecure imitation domain 'drive-- google.com’ rather than the official google.com domain. That subtle difference is a HUGE red flag. Google Docs invites will always come from a @google.com domain.
- Exercise Caution with Generic Greetings: A personalized message doesn't guarantee legitimacy, but in certain cases, generic greetings would be a cause for alarm.
- In case of a doubt, reach out to the person in question: If you doubt the legitimacy of a document share, try to get in touch with the supposed sender, but differently you already know (e.g., phone, text, separate email) so you can verify.
Remember that remaining alert and paying attention to detail will save you friction down the line. There’s a lot that can be done to double-check that the sender's address and the links seem sane to keep you away from shared document phishing scams.
Identifying The PayPal Phishing Scams
It can be scary when you get an invoice out of the blue, especially if it comes from someone whose name you recognize, like PayPal. Scammers take advantage of this anxiety to convince you to pay for something that does not exist. Here’s what you need to know to keep yourself safe.
Example Phishing Scenario:
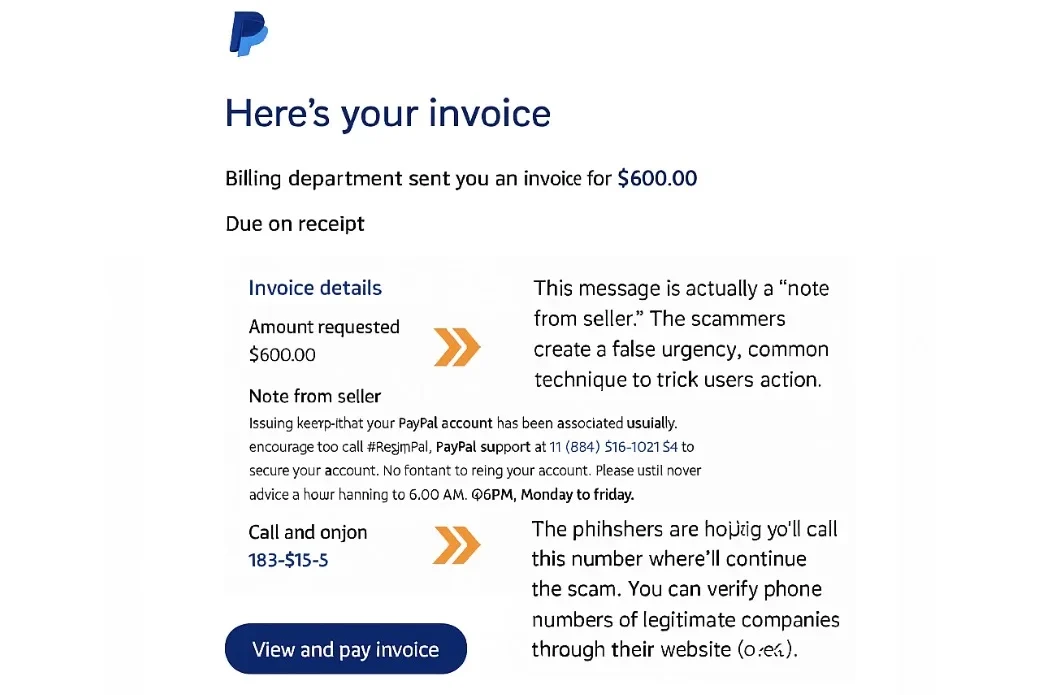
For example, an email from “Billing Department” at PayPal gets forwarded to your inbox. Attached is a $600 invoice, and the email tells you to Pay Now. Instantly.
How to Spot the Phish:
- NOTE for the seller: This is a typical ‘note from seller’. Scammers employ this strategy for communicating with recipients. Scammers constructed an artificial urgency, which is a usual technique to deceive users into doing an action. The urgency is alarming.
- CAUTION: Invoices May Contain Phone Numbers: The message contains a number that you can call if you do not recognize the charge. They expect you to make the call, where they will proceed with the scam. You can ensure the phone numbers of real companies on their sites. Do not, under any circumstances, call a number provided in a dubious email. Always look for the company's website to obtain the official contact numbers.
- DON'T CLICK THE LINK. Go Straight to PayPal: If you are in receipt of an invoice with unclear information, then do not click any links within the email. Rather, go directly to PayPal by opening its official website, which is: paypal.com. After logging into your profile, check your latest activities. If you do not find the invoice there, then it is highly likely that it is a scam.
- Dispute Phishing Invoices: In the case where an invoice is suspected to be input fraudulently, one should report it on PayPal without hesitation.
Always verify invoices directly through the official website of the service they claim to be from. Never call phone numbers listed in suspicious emails, and be wary of any message that creates a false sense of urgency.
Identifying Phony Google Security Notifications
Receiving an email that states someone has your password is enough to scare anyone. Scammers understand this and exploit fake security alerts to manipulate you. Here's how you can tell the difference between real Google security alerts and phishing scams.
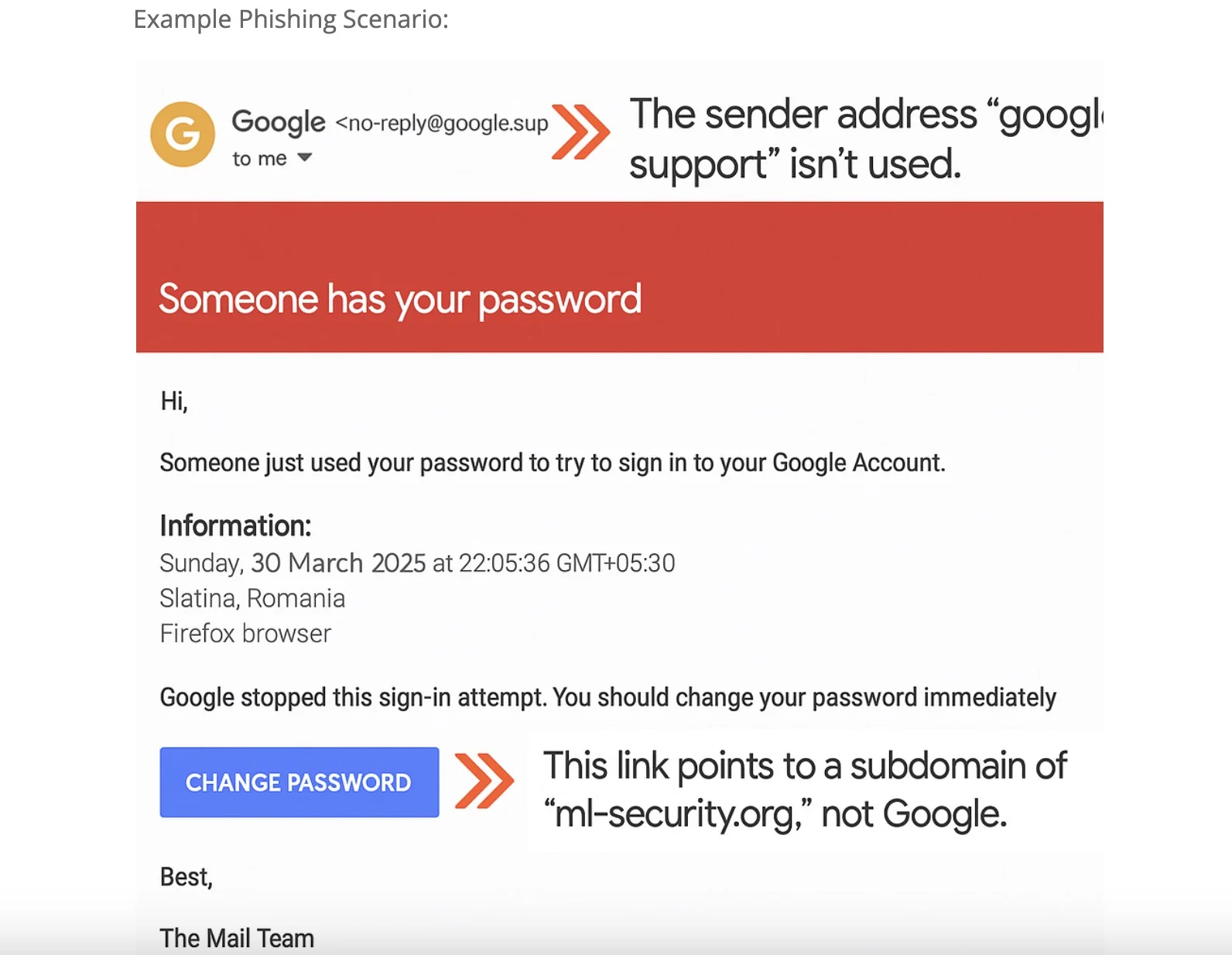
You get an email that states, “Somebody just attempted to use your password to sign into your Google Account." This message is followed by a warning to change your password right away.
How to Spot the Phish:
- Look into the Sender’s Address: The address ‘google.support’ is not one that exists. Google will send out security alerts from their own address and not a subdomain of it like ‘@support.google.com’.
- Check the Links: This link redirects to a subdomain, which is ‘ml-security.org’, which is not Google. Security Alert links must never be clicked without a thorough examination first.
- Double Check with Google: If you have any doubts, just open a new browser window and go directly to your Google Account security settings. You can check for suspicious activity or alerts on (myaccount.google.com).
- Use Caution with Urgent Requests: Google will inform you about account activity that is considered suspicious. But they will not force you to click the link to immediately change the password via email.
Scammers rely on fear and urgency to get you to act without thinking. Always verify security alerts directly through your account settings, and never click on suspicious links in emails.
Identifying the Fraudulent Google Calendar invitation
Let’s be honest, who wouldn’t want a free Pixel 7 Pro? Scammers know how to take advantage of optimistic people, and hence they promote fake contests and giveaways to effortlessly lure people into providing their sensitive personal details and the worst, credentials to their accounts.
Example Phishing Scenario:
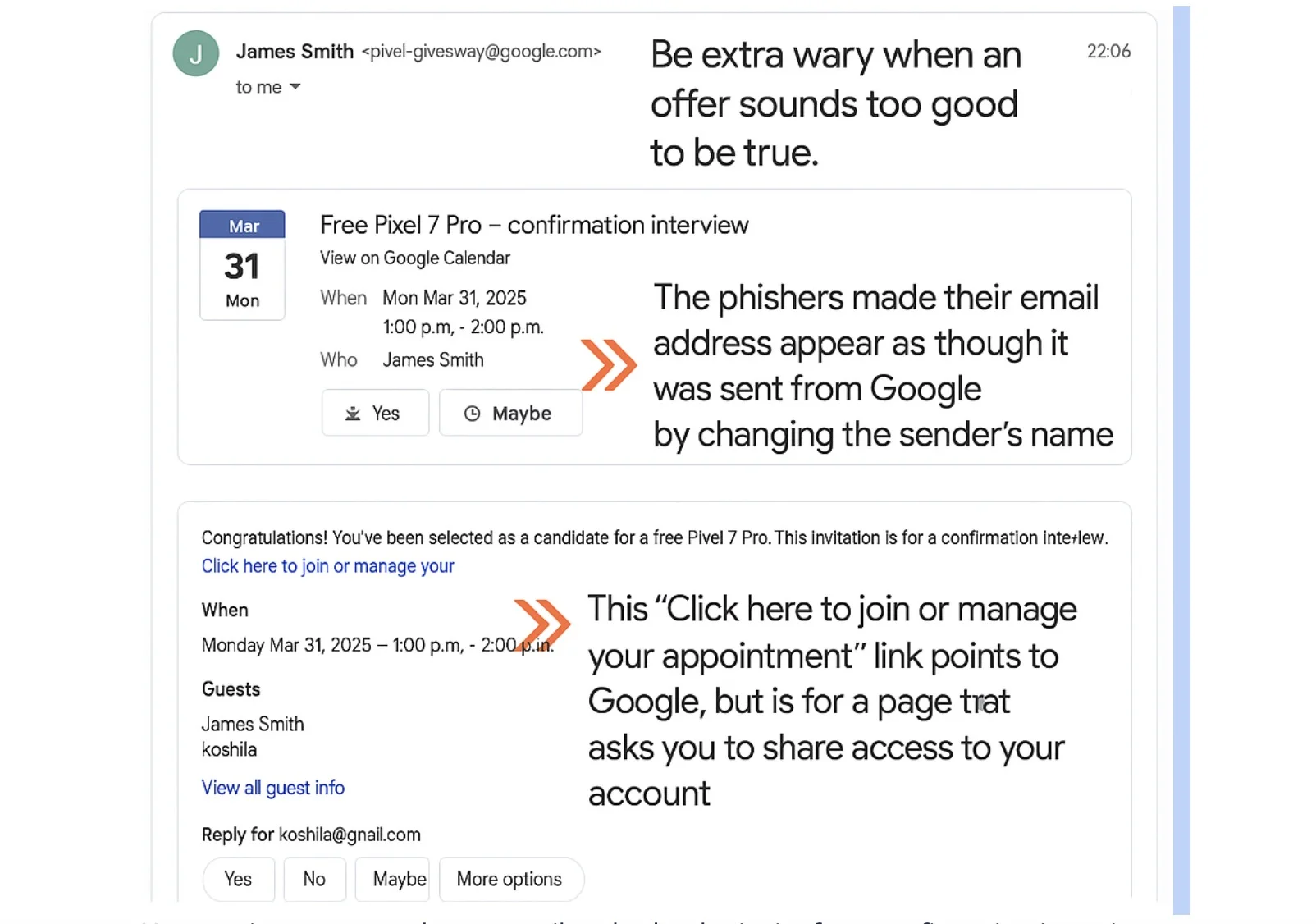
You receive a congratulatory email and calendar invite for a confirmation interview to claim your "free Pixel 7 Pro" award.
How to Spot the Phishing Scams:
- Always Be Cautioned When an Offer Looks Too Something: An offer that appears to be too good to be true probably is. There is almost always a catch, and severe, appropriate giveaways from reputable brands will never ask you for sensitive account details.
- Examine Sender’s Email: When receiving the phishing email, the sender’s email already showed that it is “sent from Google,” while in truth, they only changed the sender’s name.
- Check the Links: The link ‘Click here to join or manage your appointment’ directs to Google, while it is a page that invites you to grant account access. Almost all contests or giveaways do not require sharing account access.
- Avoid Sharing Account Access: Google is among the tech companies whose users need to be very careful in granting accounts to third parties.
Always be skeptical of unsolicited offers, especially those that seem too good to be true. Carefully examine links before clicking, and never share your account credentials or grant access to your account unless you are certain the request is legitimate.
Best practices for email protection to avoid phishing and other email-based scams
- Spot phishing scams by checking the following:
- The email makes unrealistic threats or demands (such as "URGENT" or "Your service will be terminated immediately unless...")
- There's a catch at the end (such as a demand for fees or credentials)
- Poor spelling and grammar
- A mismatched or unverified URL
- You are asked for sensitive information
- There is a suspicious attachment (even normal attachment types are suspicious if you weren't expecting an attachment, and things like .zip are a way to avoid malware scanning)
- Do not perform any sensitive transactions via email, especially unsolicited financial transactions or credential-related requests (unrequested password resets, accessing unexpected documents, etc.). Always go directly to the official website or app.
- Mark phishing emails using Gmail's "Report Phishing" feature. (Steps are specific to Gmail; adjust for other email providers.)
- Open the message
- Next to "Reply," click "More" (usually represented by three vertical dots)
- Click "Report Phishing"
General Tips for Staying Safe
- Enable Multi-Factor Authentication (MFA): This adds an extra layer of security to your accounts.
- Use Strong, Unique Passwords: Don't reuse passwords across multiple sites. Use a password manager to help.
- Keep Your Software Updated: Software updates often include security patches that protect against the latest threats.
- Think Before You Click: Always be cautious about clicking on links in emails, especially if you weren't expecting them.
- Trust Your Gut: If something feels off, it probably is.
Remaining internationally suspicious while keeping up to date with email security frameworks can aid in keeping the user significantly less prone to phishing scams. Take utmost care while examining an email, validating the information through proper sources, and always refrain from disclosing sensitive information unless proper groundwork supports it. Ensure that this guide is shared amongst friends so that they can stay securely online as well.